Is this Crown Sterling press release from another planet?
There are press releases. Then there are out of body experiences.
Cryptography firm Crown Sterling announced a new product called Time AI. It leaves ordinary buzzwords like “seamless” and “omnichannel” in the dust, reaching instead for a heady mix of mathematics, quantum computing, mysticism, and privacy handwringing.
Let’s take a look. Commentary is mine.
Crown Sterling Unveils TIME AI™ – the World’s First ‘Non-factor’ Based Quantum Encryption Technology at Black Hat 2019
Crown Sterling’s Revolutionary TIME AI™ Technology Enables Data Sovereignty for Consumers and Enterprises Globally
August 07, 2019 12:00 PM Eastern Daylight Time
LAS VEGAS–(BUSINESS WIRE)–Crown Sterling, a leading digital cryptography firm, today unveiled TIME AI™, the world’s first dynamic ‘non-factor’ based quantum AI encryption software to protect data privacy for consumers and enterprise systems – www.timeai.io. TIME AI™ is based on the recent discovery from Crown Sterling’s Founder and CEO, Robert E. Grant, in which he recently identified the first Infinite Prime Number prediction pattern.
For those keeping track at home, score extra points for the buzzwords “quantum AI encryption,” “data sovereignty,” and one weasel word point for “revolutionary.”
But it’s got math!
As it turns out, I studied number theory in college and in the Ph.D. math program at MIT, so I’m not exactly an amateur here. So I can tell you that prime number prediction is not really a thing. Prime numbers obey certain patterns just by virtue of their not having factors, but there is no way to predict them. You can statistically predict their distribution, and you can prove some facts about them, but there is no way to predict them. (I might also mention that the computational challenge of identifying primes and prime factors is the basis for all modern cryptography, so if there was an easy way to predict which numbers were prime, the whole basis of cryptography would collapse. You can imagine how much effort has gone into that question as a result.)
Utilizing multi-dimensional encryption technology, including time, music’s infinite variability, artificial intelligence, and most notably mathematical constancies to generate entangled key pairs, TIME AI™ is designed to wrap around all data and applications to secure the world’s most valuable asset — data. Crown Sterling is demonstrating TIME AI™ this week at Black Hat 2019 in Las Vegas at the Mandalay Bay Convention Center, Booth Number 1304.
Potentially qualifies as the most surreal sentence to ever appear in a press release. “Time, music’s infinite variability, artificial intelligence, and most notably mathematical constancies to generate entangled key pairs” — yeah, that’s the kinda stuff that doesn’t occur to you until after your third LSD trip. The technical term for this form of language is “woo-woo.”
“Today’s introduction of Crown Sterling’s TIME AI™ will transform the way we secure data, currently the world’s most valuable asset,” said Grant. “We believe whomever creates the data leading to its value should have the ability to control it and its value creation. Consumers’ primary concerns are privacy and identity theft, while enterprises value data security. Either way, they face the same challenge: how to better protect and control their data and its dissemination.”
If this is as revolutionary as you say, there’s no need to wrap yourself in the clothing of a privacy advocate. Data needs security. Nobody gives a crap about your libertarian ideals around it.
In March of 2019, Grant identified the first Infinite Prime Number prediction pattern, where the discovery was published on Cornell University’s www.arXiv.org titled: “Accurate and Infinite Prime Number Prediction from Novel Quasi-Prime Analytical Methodology.” The paper was co-authored by Physicist and Number Theorist Talal Ghannam PhD. The discovery challenges today’s current encryption framework by enabling the accurate prediction of prime numbers.
Grant will also give a presentation at Black Hat titled, “Discovery of Quasi-Prime Numbers: What Does this Mean for Encryption?” related to his paper published through Cornell University.
So I read the paper for you. My impression is that it is a naive analysis reflecting some basic patterns that would be clear from taking the 101-level number theory course, combined with some noodling around “digital roots” (which are dependent on our base-10 numbering system, and therefore not all that relevant to a paper regarding numbers in general). The paper is not peer reviewed, and I don’t expect it to survive peer review.
But it does have a beautiful picture in it, which I have reproduced below.
I don’t imagine this breakthrough will actually revolutionize data security. But it has already broken new ground in press releases, so who knows.
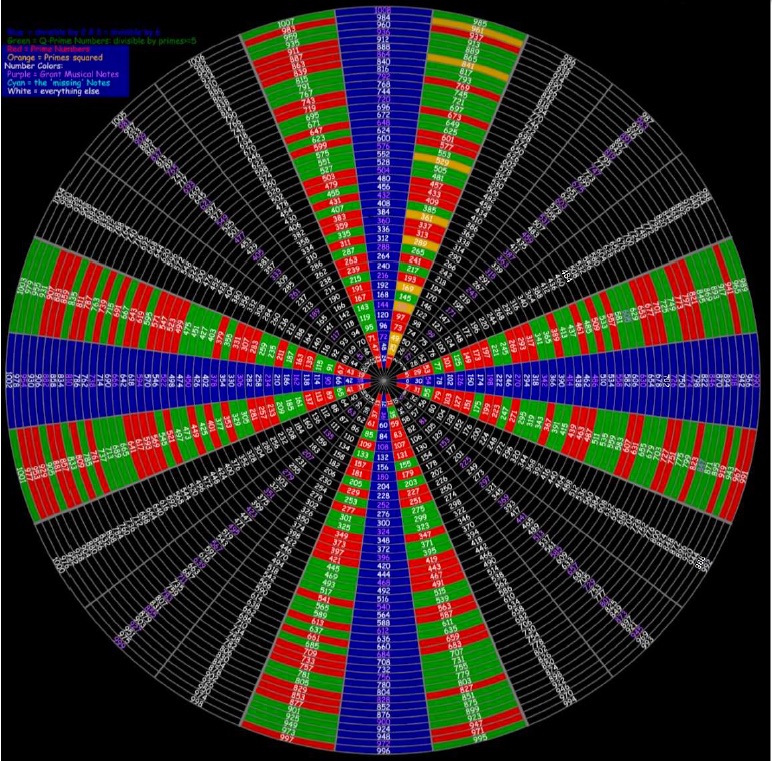
Analytical Methodology” by Robert E. Grant and Talal Ghannam.
Mr. Grant’s sponsored presentation at Black Hat (hacker/cybersecurity conference) last week created a sizable kerfuffle on Twitter. Interested readers might enjoy the impassioned exchanges.
https://twitter.com/dguido/status/1159575196015026177?s=19
Found this video which is even more surreal.
Okay, I’ll bite. Not being a numbers person at all, I want to start with a couple of basic questions. First, aren’t all prime numbers just prime numbers (divisible only by themselves and one) and if you have a calculator — or computer — you can just do the math to figure out the next one? I don’t know why one would, but I don’t know why I had to learn most of Algebra, either.
And, assuming that’s the case (and I know it may not be because of that not being a numbers person and all), what the hell do prime numbers have to do with whether or not data can be encrypted? Is it like they’ve invented some sort of padlock that you can’t open unless you can do long-range imaginary math that has no real-world application, like figuring out how many dog years it takes to get to Alpha Centauri or similar?
And finally, what PR person could have possibly been persuaded to issue a press release that even the world’s best grammarians couldn’t proofread since no one other than lab nerds can understand — much less spell — 75% of that gobledy-goo?
Since you understand math, perhaps you can help me on the first two questions. I think I can imagine the answer to the third. Heh.
Jason, I’ll explain. While in theory, finding the next prime number is a simple matter of arithmetic, in practice, it requires a great deal of computation. The basis for modern cryptography is that if you know the two prime factors of a large number, you can use that to decode the message, but only those who know the numbers can decode the message. While those who don’t know the numbers could figure them out with arithmetic, that arithmetic might take hundreds of years.
This is why statements about making it far easier to find prime numbers could have a major impact on cryptography. If you had a magic wand that would reduce the amount of computation by a factor of a hundred or a million, you could decode every secret message or break into every financial system and do whatever you wanted.
Hilarious takedown.
There appears to be some modestly-long-term collaboration between Grant and a reported academic named Talal Ghannam (laureate of Western Michigan University, completing his photonic-physics dissertation under Dr. Alvin Rosenthal in ~2007). Ghannam’s post-doctorate career spans a year of intro-Physics lectures at WMU, followed by ~7 years’ unspecified research at King Saud University in Riyadh; from 2015 onward, he is tightly coupled with Grant, first via Strathspey Holdings, and now Crown Sterling. This has bearing, because Grant purports to have somehow fused “photonic uniqueness” with “musical phenomena” and “new-pseudo-prime algorithms” to fuel his revolutionary crypto. Both gentlemen list art/music/comic-book illustrator hobbies as foremost in their list(s) of respective talents. Theranos, redux.
Fascinating topic. I live in Orange County, met Robert, and was fascinated with the pattern of primes he found (which is reproduced in the picture you published). Apparently by putting all numbers from 1 to N into a circular pattern with 24 columns, all two digit primes or greater fall into the two columns on either side of the horizontal and vertical axis. I do not know why this is, maybe it is a known to others but I have never seen a paper with this picture with these findings. Are you implying it is widely known – or is not true? Obviously it greatly reduces the search area when looking for primes. Love to know the reason that primes fall into these particular columns? Can you direct us to any papers that address the why of this pattern? Very Curious.
It is obvious to any number theorist. Not a significant finding.
Could you please elaborate Josh? Not everyone is a number theorist. People need each other you know
Here’s a simpler one:
Every integer N has one of the following 6 forms (with k being an integer)
– 6k
– 6k+1
– 6k+2
– 6k+3
– 6k+4
– 6k+5
(saying this is equivalent of arranging numbers on a wheel with 6 “spokes”)
6k, 6k+2 and 6k+4 cannot be prime prime as they can be divided by 2, for example, 6k+2 = 2*(3k+1)
6k, 6k+3 cannot be prime either (can be divided by 3)
So we’ve just proven that all prime numbers can only be of the form 6k+1 or 6k+5. So, on this “wheel”, all prime numbers are on these 2 “spokes”, while the other 4 spokes won’t have prime numbers (except 2 and 3).
On a wheel with 24 “spokes”, the proof is similar, just a little longer to write due to more cases to consider.
FWIW this is taught in high school in my country
I know that at least one Grant “colleague”
Has a very legitimate background and a very stable years-longs series of historically significant research projects. ( in my opinion.). “ I hope Grant is not abusing the relationship “ is a fair statement. People like Grant have many sides, i would assume, perhaps not great in cryptology terms, but hopefully positive in terms of real friendship and collaboration. Jury out, evidence poring in.
Been following these people for a while now. It’s all BS.